Halloween is just a few days away. And spooky season in full swing. There are lots of tricks, and hopefully more treats going around for everyone to share. Unfortunately, there’s one trick that seems to be increasing in recent years, cybercrimes and related issues. October is also International Cyber Security Awareness Month. That means there’s no better time than now to debunk the cyber scares and ensure that your business is safe and secure online.
Editors note: In light of Data Privacy Day 2022, we’re revisiting this article with the tips to make your organization more safe and secure when it comes to protecting your data.
So not as to frighten you, but rather help you, we sat down with our resident Cyber security expert, Olu Asaolu, Senior Information Security Analyst at Oneflow to raise awareness about all things cyber security. We’ll start with the basics.
What is cyber security?
Cyber security is the protection of computer systems and networks from unauthorized access, information disclosure, theft, or damage to hardware, software, or electronic data that would impede the services that they provide. It’s the practice of managing digital assets and keeping them safe. Think of the traditional methods of protecting physical assets, for example, a home security system protecting your house or banks holding cash and gold in thick storage vaults. Those exist in the cyber world as well. Simply stated, they’re measures put in place to safeguard a business or organization from cyber attacks.
This is especially important because more and more of the world relies on services provided through the internet. A great example of this reliance is when Google, and most recently Facebook suffered outages that affected millions of users and businesses alike. While there’s no evidence showing that those instances were due to a hack, it still highlights how pivotal the internet is to the core functions of a modern business. When it comes down to it, having vital data and key business capabilities hosted on a cloud server means that their security should be an absolute priority. But in order to keep your organization safe, you’ve gotta know what the strategies of cyber attackers are.
Common tactics of cyber attackers
Phishing
The main tactic hackers regularly employ is phishing. This is when a cyber attacker sends out an innocuous-looking email or message that has the goal of revealing sensitive information about the organization. It usually appears to be an email from someone inside the company, a typical cold outreach email, or the like. According to Olu, these emails are quite sophisticated but manageable if your employees are trained to spot them.
“A main threat and tactic is phishing. Where they (attackers) are starting to be more sophisticated and targeted in their efforts. Meaning that they aren’t sending out mass emails, but are specifically targeting certain companies and individuals within them.” Olu goes on to say, “We’ve established safety parameters to identify them before they get through, but in the occurrence that they do our employees are well trained to know how to spot a phishing email.”
Ransomware is when a company infiltrates a system, encrypts its files, and locks them until the company pays a ransom. This is a common strategy employed today and usually starts with a phishing email says Olu.
Data decay
Another area of focus by hackers that can lead to a cyber attack is data decay. This is a cause of concern because like all other things, data degrades over time. Unless this data is properly updated, managed, and kept safe and secure, it can be taken advantage of while a company is none the wiser. A malicious actor could recognize outdated or defective data and then use that as an entry point to breach into their system. It’s concerning because it’s easy to overlook the rot or the decay in data according to Olu. It’s a bit of a silent killer.
Exploiting user error
This is a tactic that is hard to 100% defend against, but of course, you can do it. However, as long as humans are alive, we are going to make errors and simple mistakes. What this means when it comes to cyber security is that someone within the company can use a personal password or a simple password for their work access. Then, if that password gets caught up in a leak, it’s possible that a malignant actor then has the key to get into their organization’s system.
According to Olu, you can prevent this with two-factor authentication for your passwords. But strictly speaking, you can’t force people to not use personal passwords. It’s up to them to come up with one that suits their needs. As people are different and do things their own way, it’s hard to guarantee that an error won’t slip through the cracks. Passwords end up in leaks all the time so this is a tactic that’s likely to be relevant for the foreseeable future. But if your organization doesn’t have guidelines on how to make a difficult password, you can always check to see if a computer can guess it.
With these tactics in mind, it’s time to figure some ways to keep your company safe from cyber threats.
Steps to shore up your cyber security
Security is of utmost importance. Regardless of the situation or context. If you’re not safe, you’re not going to be able to do what you’re trying to do. In business, this means providing a good or service to your customers. However, according to Olu, there are a few steps that a company can take to keep itself safe from the growing threat of cyber attacks.
Protocols
The first step is having a proper cyber security set up to protect your network and systems. A move in the right direction is employing a security analyst, and establishing protocols that safeguard your business. It could be creating a spam filter to prevent harmful emails from getting into employees’ mailboxes. Or creating a block against aggressive actions such as a DDOS attack. It’s about having the right safeguards in place and people in those positions to protect your business from harmful actors. This can include creating a full-scale vulnerability management program, codifying and formalizing how to cope with threats.
Employee Awareness
The second step according to Olu is to educate and make your employees aware of the common tactics employed by cybercriminals. This means having online classes at regular intervals so that employees know what tactics and strategies are being employed by cyber attackers. It creates a base-level understanding of how to spot sketchy activity and what to do if they suspect something is a bit fishy. It creates another layer of protection to keep your organization safe.
Backups for your backups
Every digital and online asset that your business uses should be saved to the cloud or have a backup located on an external drive according to Olu. This is because, in the worst-case scenario, you’ll still have all of your information readily available for use.
“If you have everything backed up on an external hard drive, or saved to the cloud you’re safer. That’s because, in the chance that you’re affected by ransomware, you can kill the machine or drive and start over with those backups, as you’ll still have those files. You can eliminate that threat entirely by simply having backups,” says Olu.
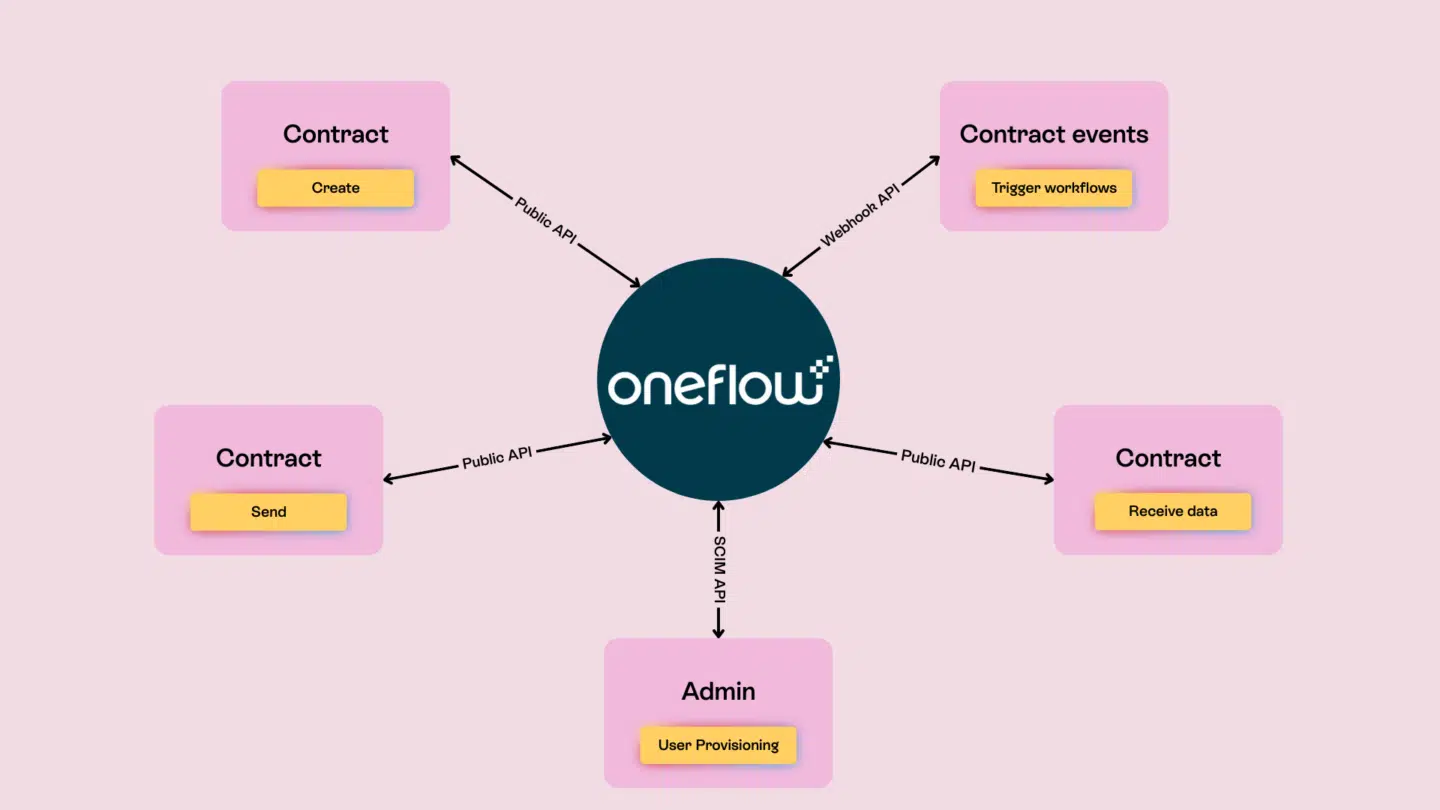
This cloud safety feature is of extreme importance for Oneflow and its customers says Olu. Oneflow is a cloud organization. That means that if any of your customers were affected by ransomware then you can rest easy because all of your contracts and agreements will be safe.
How to keep your data private
There are a few sound and great tips from the National Cyber Security Alliance on how to keep your data safe, secure, and private in the digital world that we live in. Data privacy is a topic that is always relevant, but with an increased focus due to ongoing regulations such as GDPR, it’s a good time for a refresher on how to stay safe online. Let’s look into the wise advice from StaysafeOnline.org:
For individuals:
- Keep it private
- Understand the privacy/convenience tradeoff
- Manage your privacy
- Protect your data
For businesses
- Respect privacy
- Conduct an assessment
- Adopt a privacy framework
- Educate employees
Cyber security tips, boiled down
If we boil it down to a few key components that can keep your organization and business safe from malicious cyber attacks, there are five that stand out. In no particular order, here they are according to Olu:
- Education and awareness: You employees should know what threats are out there and have a basic understanding of them and how they work.
- Invest in cybersecurity software that are able to detect threats: You should also have sufficient and accurate logs within your system so that you can track access and determine who did what, and when. Logging as a service (LaaS), for example, is a way to track activity internally, while a threat intelligence platform automates analysis and investigation of security issues.
- Proper processes and workflow instructions: risks are mainly introduced because of user errors. While it’s hard to eliminate those entirely, if processes are established then it creates more margin for error amongst your employees.
- Penetration testing: Have your internal teams, or look external to check your networks. Determine the true security of it. Annually test codes before putting them into production. It’s a boon to have penetration testers that understand development as well. Better yet, use a pentesting automation solution to speed up and simplify this mission-critical process. This will allow human testers to work faster and more thoroughly than before when probing for vulnerabilities.
The last but surely not least takeaway of Cyber Security Awareness month is one of the most important. Cyber strategy is not a one-off exercise. If you want to ensure that your organization is completely safe, it starts, as usual, with the culture. Senior management should buy into the initiatives and safety aspects so that people take them seriously. You need to make it become a culture and thought process that is ingrained in the entire organization.
Looking for a safe and secure contract management solution? Check out Oneflow, for free!